Discussions about cybersecurity often focus on how effective defense can help limit the impact of attacks once cybercriminals have breached your network. Although this is a critical aspect of effective security, the advantages of cybersecurity extend beyond better reactions to help companies proactively protect digital assets from potential attacks.
Common cybersecurity mistakes businesses continue to make

Since last year’s biggest cyberattacks did not spare big names such as Facebook and British Airways, you’d think that small- and medium-sized businesses (SMBs) would take more serious precautions against cybercrimes. Yet the opposite is true. Cybercrime rates continue to rise, with 58% of victims categorized as SMBs. And while this trend is due in part to the more advanced tactics employed by cybercriminals, the biggest factors to the success of cybercrimes are the counterproductive security practices that businesses cultivate.
Three serious BYOD security risks every business owner should know about
Disaster recovery statistics business owners need to know
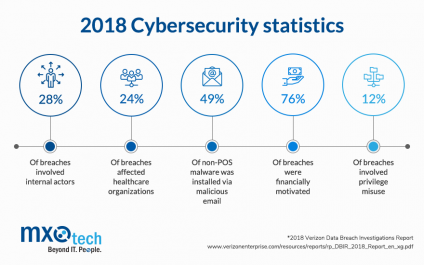
All businesses hold confidential client data and information that will fetch a hefty sum on the black market, so no industry is completely safe from financially-motivated cyber attacks. For example, the health industry is full of valuable data like Social Security numbers, and as per Verizon’s 2018 Data Breach Investigations Report, data breaches affected one in four healthcare organizations.
Creating an engaging cybersecurity training program
Top 4 reasons you need to train your employees on cybersecurity
6 password policy requirements to help Chicago companies avert attacks
Your organization can take every precaution to prevent against a cyberattack — firewalls, anti-virus, anti-malware, spam filter, etc. But your biggest liability isn’t lurking in the cyber shadows: they’re sitting in your office. And failing to enforce employee password policy requirements could put your company data at risk.
Here are tips from Will, our Director of Support Services, including best practices to help prevent hacks, the password storage tool he recommends, and more.
How to keep your employees from leaking confidential information

Back in 2014, Code Spaces was murdered. The company offered tools for source code management, but they didn’t have solid control over sensitive information — including their backups. One cyberattack later, and Code Spaces was out of business. Their killer had used some standard techniques, but the most effective was getting an unwitting Code Space employee to help — likely via a phishing attack.
For Chicago Businesses: The 9-Step Security Checklist to ensure safe, recoverable data

It seems like the news mentions a new cyberattack or cyber threat almost daily, so how could you possibly relax knowing that these innovative and creative hackers are constantly designing new ways to catch you and your data off-guard? A well-designed secure computer network can give you the confidence that “all systems are go,” whether you’re at home or in the office.





