Since last year’s biggest cyberattacks did not spare big names such as Facebook and British Airways, you’d think that small- and medium-sized businesses (SMBs) would take more serious precautions against cybercrimes. Yet the opposite is true. Cybercrime rates continue to rise, with 58% of victims categorized as SMBs. And while this trend is due in part to the more advanced tactics employed by cybercriminals, the biggest factors to the success of cybercrimes are the counterproductive security practices that businesses cultivate.
Common cybersecurity mistakes businesses continue to make
Three serious BYOD security risks every business owner should know about
What is a test automation framework?

A test automation framework is a set of rules, guidelines, and tools for testing software products under development. It helps quality assurance teams improve both their productivity and user experiences. With a well-documented framework, organizations can test new software deployments more thoroughly, mitigate human error, and save time using automation.
How technology integration can help your business flourish

Modern businesses rely on various technologies to keep their companies up and running. Today, most of them need an internet connection and multiple apps and software to help their staff get things done.
At first glance, all the different technologies you use may seem unrelated to one another — after all, the software your accounting department uses is different from what your research and development team has and so on.
Best practices for a successful security awareness training program

Film and television perpetuate the idea of one high-profile hacker getting through a company’s cybersecurity and stealing confidential data, but most data breaches aren’t that exciting: more often than not, the culprit is closer to home.
In the 2018 study by the Ponemon Institute, 61% of the respondents pinned the cause of data breach to a negligent employee (an alarming 112.9% increase from 2017). A properly researched and well-executed security awareness training can help lower the risks of data breaches caused by internal factors.
Continuous integration and continuous delivery in web application development

From client information management to automated billing and accounting, businesses turn to custom web applications to solve the problems that cause bottlenecks in their workflows. Companies invest a lot of time and money to have developers build such bespoke apps, so it can be utterly frustrating to find out that critical functions don't work upon deploying the apps into the real world.
Disaster recovery statistics business owners need to know
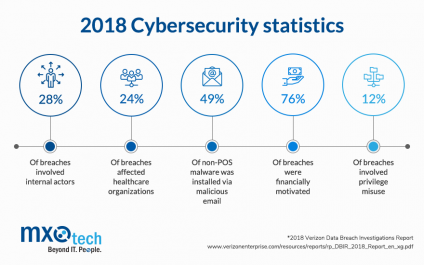
All businesses hold confidential client data and information that will fetch a hefty sum on the black market, so no industry is completely safe from financially-motivated cyber attacks. For example, the health industry is full of valuable data like Social Security numbers, and as per Verizon’s 2018 Data Breach Investigations Report, data breaches affected one in four healthcare organizations.
What is test driven development and what does it mean for your business?

By Sean Blair,
CTO at MXOtech
The only way for a business to survive in a world dictated by fast-changing technology is to evolve with it. A business must learn to improve its existing technology to remain competitive. How can this be done? We can learn a thing or two from the principle of test driven development (TDD).
What is TDD?
TDD is a software development process that takes small steps instead of rolling out big changes at once.
How to Create a Customer-Obsessed Culture

by Joanna Mirov
One of my favorite people is Nido Qubein. For those of you who don’t know, he’s a businessman, motivational speaker, and the President of High Point University in High Point, North Carolina. Nido places extreme importance on providing his students and their families with extraordinary experiences.
MXOtech Takes Healthcare Solutions to the Next Level with New HITRUST Certification

Many successful small businesses have one thing in common — the ability to see the big picture, envision what their success will look like tomorrow, and invest in it today.
At MXOtech, a boutique, women-owned IT solutions firm specializing in custom healthcare development solutions, this is definitely the case.



